网关服务器和网站服务器都采用centos 7操作系统;网关服务器安装3块千兆网卡,分别连接在Internet、企业内网、网站服务器。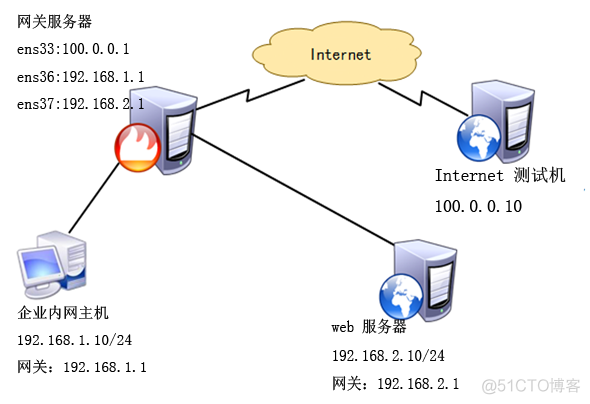 要求如下:网关服务器连接互联网卡ens33配置为公网IP地址,分配到firewall的external区域;连接内网网卡ens37地址为192.168.1.1,分配到firewall的trusted区域;连接服务器网卡ens38地址为192.168.2.1,分配到firewall的DMZ区域。网站服务器和网关服务器都通过SSH来远程管理,为了安全,将SSH默认端口改为12345。网站服务器开启https,过滤未加密的http流量。网站服务器拒绝ping,网关服务器拒绝来自互联网上的ping。内网用户需要通过网关服务器共享上网。互联网用户需要访问网站服务器。基本的环境配置:网关服务器配置 网卡 :
要求如下:网关服务器连接互联网卡ens33配置为公网IP地址,分配到firewall的external区域;连接内网网卡ens37地址为192.168.1.1,分配到firewall的trusted区域;连接服务器网卡ens38地址为192.168.2.1,分配到firewall的DMZ区域。网站服务器和网关服务器都通过SSH来远程管理,为了安全,将SSH默认端口改为12345。网站服务器开启https,过滤未加密的http流量。网站服务器拒绝ping,网关服务器拒绝来自互联网上的ping。内网用户需要通过网关服务器共享上网。互联网用户需要访问网站服务器。基本的环境配置:网关服务器配置 网卡 :
启动网关服务器上的路由转发功能:
[root@localhost /]# vim /etc/sysctl.conf net.ipv4.ip_forward = 1 [root@localhost /]# sysctl -p net.ipv4.ip_forward = 1配置 web 服务器的网卡:
[root@localhost /]# ip a 2: ens33: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc pfifo_fast state UP qlen 1000 link/ether 00:0c:29:2f:24:4b brd ff:ff:ff:ff:ff:ff inet 192.168.2.10/24 brd 192.168.2.255 scope global ens33 valid_lft forever preferred_lft forever inet6 fe80::19de:d9a7:568a:f34f/64 scope link valid_lft forever preferred_lft forever [root@localhost /]# route -n Kernel IP routing table Destination Gateway Genmask Flags Metric Ref Use Iface 0.0.0.0 192.168.2.1 0.0.0.0 UG 100 0 0 ens33Internet 测试机网卡配置:
[root@localhost /]# ip a 2: ens33: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc pfifo_fast state UP qlen 1000 link/ether 00:0c:29:45:66:64 brd ff:ff:ff:ff:ff:ff inet 100.0.0.10/8 brd 100.255.255.255 scope global ens33 valid_lft forever preferred_lft forever inet6 fe80::3ebc:8f75:cd28:e516/64 scope link tentative valid_lft forever preferred_lft foreverweb 服务器环境搭建:
[root@localhost ~]# systemctl start firewalld #启动防火墙 [root@localhost ~]# yum -y install httpd mod_ssl #安装httpd和mod_ssl [root@localhost ~]# systemctl start httpd #启动httpd服务 [root@localhost ~]# systemctl enable httpd #设置为开机自启 [root@localhost ~]# vim /var/www/html/index.html #新建网站测试首页文件 test.com [root@localhost ~]# vim /etc/ssh/sshd_config #更改SSH的侦听端口(需关闭SELinux): ................ Port 12345 ................ [root@localhost ~]# systemctl restart sshd在网站服务器上配置firewalld防火墙:1、设置默认区域为dmz区域:
[root@localhost ~]# firewall-cmd --set-default-zone=dmz success2、为dmz区域打开https服务并添加tcp的12345端口:
[root@localhost ~]# firewall-cmd --zone=dmz --add-service=https --permanent success [root@localhost ~]# firewall-cmd --zone=dmz --add-port=12345/tcp --permanent success3、禁止ping:
[root@localhost ~]# firewall-cmd --add-icmp-block=echo-request --zone=dmz --permanent success4、因为已经更改了预定义SSH服务的默认端口,所以将预定义SSH服务移除:
[root@localhost ~]# firewall-cmd --zone=dmz --remove-service=ssh --permanent success5、重新加载firewalld配置,并查看之前的配置:
[root@localhost ~]# firewall-cmd --reload success [root@localhost ~]# firewall-cmd --list-all dmz (active) target: default icmp-block-inversion: no interfaces: ens33 sources: services: https ports: 12345/tcp protocols: masquerade: no forward-ports: source-ports: icmp-blocks: echo-request rich rules:网关服务器上配置firewalld防火墙:1、将网卡添加至指定区域:
[root@localhost /]# systemctl start firewalld #启用防火墙 [root@localhost /]# firewall-cmd --set-default-zone=external #设置默认区域为external success [root@localhost /]# firewall-cmd --change-interface=ens37 --zone=trusted #将ens37添加至trusted区域 The interface is under control of NetworkManager, setting zone to 'trusted'. success [root@localhost /]# firewall-cmd --change-interface=ens38 --zone=dmz #将ens38添加至dmz区域 The interface is under control of NetworkManager, setting zone to 'dmz'. success2、查看配置,并保存为永久
[root@localhost /]# firewall-cmd --get-active-zones dmz interfaces: ens37 external interfaces: ens33 trusted interfaces: ens36 [root@localhost /]# firewall-cmd --runtime-to-permanent # 将当前的配置保存到文件中 success3、在企业内部主机上测试: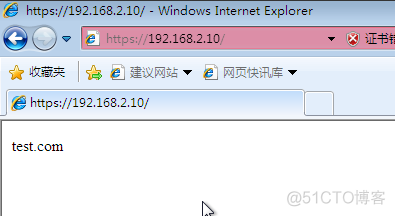
4、更改SSH的侦听端口,并重启服务(需关闭SELinux):
[root@localhost ~]# vim /etc/ssh/sshd_config ................ Port 12345 ................ [root@localhost ~]# systemctl restart sshd5、配置external区域添加tcp的12345端口:
[root@localhost /]# firewall-cmd --zone=external --add-port=12345/tcp --permanent success6、external区域移除SSH服务:
[root@localhost /]# firewall-cmd --zone=external --remove-service=ssh --permanent success7、配置external区域禁止ping:
[root@localhost /]# firewall-cmd --zone=external --add-icmp-block=echo-request --permanent success8、重新加载防火墙配置:
[root@localhost /]# firewall-cmd --reload success测试ssh连接:在 Internet 测试机通过SSH连接网关服务器的外部接口地址的12345端口:
[root@localhost /]# ssh -p 12345 100.0.0.1 The authenticity of host '[100.0.0.1]:12345 ([100.0.0.1]:12345)' can't be established. ECDSA key fingerprint is 68:df:0f:ac:c7:75:df:02:88:7d:36:6a:1a:ae:27:23. Are you sure you want to continue connecting (yes/no)? yes Warning: Permanently added '[100.0.0.1]:12345' (ECDSA) to the list of known hosts. root@100.0.0.1's password: Last login: Sun Sep 1 16:36:33 2019 [root@localhost ~]#使用内网测试机SSH登录web网站服务器的12345端口:
[root@localhost /]# ssh -p 12345 192.168.2.10 The authenticity of host '[192.168.2.10]:12345 ([192.168.2.10]:12345)' can't be established. ECDSA key fingerprint is 68:df:0f:ac:c7:75:df:02:88:7d:36:6a:1a:ae:27:23. Are you sure you want to continue connecting (yes/no)? yes Warning: Permanently added '[192.168.2.10]:12345' (ECDSA) to the list of known hosts. root@192.168.2.10's password: Last login: Sun Sep 1 16:36:39 2019 [root@localhost ~]#实现 IP 伪装与端口转发:1、在Internet测试机上搭建web服务,用来测试:
[root@localhost ~]# yum -y install httpd [root@localhost ~]# vim /var/www/html/index.html www.baidu.com [root@localhost ~]# systemctl enable httpd [root@localhost ~]# systemctl start httpd2、在内部测试机和dmz的网站服务区都可以访问外网的网站(若访问不了,则可能是公网测试机的防火墙配置问题,可先将公网测试机的防火墙关闭,或放行相关服务的流量即可):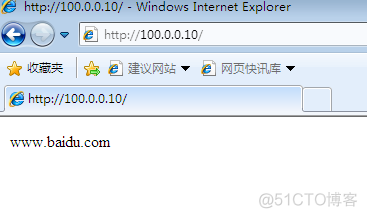 3、查看网关服务器的external区域是否开启了地址伪装:
3、查看网关服务器的external区域是否开启了地址伪装:
4、只为源地址192.168.1.0/24网段的地址开启地址IP伪装。在网关服务器上关闭external默认的地址伪装,添加富规则,要求external区域内,源地址为192.168.1.0/24网段的地址开启地址IP伪装:
[root@localhost ~]# firewall-cmd --remove-masquerade --zone=external success [root@localhost ~]# firewall-cmd --zone=external --add-rich-rule='rule family=ipv4 source address=192.168.1.0/24 masquerade' success在dmz区域上测试访问发现无法访问,但内网主机却可以:
[root@localhost /]# curl http://100.0.0.10 curl: (7) Failed connect to 100.0.0.10:80; No route to host5、配置端口转发实现互联网用户可以访问内部web服务器:在网关服务器上配置:
[root@localhost /]# firewall-cmd --zone=external --add-forward-port=port=443:proto=tcp:toaddr=192.168.2.10 success在Internet测试机上访问内网的web服务器成功: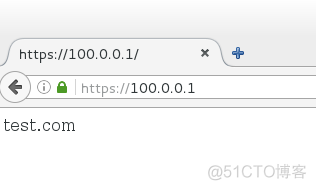 六、使用富规则实现端口转发:
六、使用富规则实现端口转发:
上述配置完成后,若现在公司申请了一个新的公网ip地址100.0.0.254,那么就需要重新做端口转发了:
1、将新申请的公网地址100.0.0.254配置在网关服务器的外网接口ens33上,作为第二个IP地址:
[root@localhost /]# vim /etc/sysconfig/network-scripts/ifcfg-ens33 TYPE=Ethernet BOOTPROTO=static IPADDR0=100.0.0.1 # 改到下四行 PREFIX0=24 IPADDR1=100.0.0.254 PREFIX1=24 # 添加成两个IP DEFROUTE=yes PEERDNS=yes PEERROUTES=yes IPV4_FAILURE_FATAL=no IPV6INIT=yes IPV6_AUTOCONF=yes IPV6_DEFROUTE=yes IPV6_PEERDNS=yes IPV6_PEERROUTES=yes IPV6_FAILURE_FATAL=no IPV6_ADDR_GEN_MODE=stable-privacy NAME=ens33 DEVICE=ens33 ONBOOT=yes ZONE=external [root@localhost /]# ifdown ens33;ifup ens33 # 重启网卡使配置生效 [root@localhost /]# ip a # 查看配置是否成功 2: ens33: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc pfifo_fast state UP qlen 1000 link/ether 00:0c:29:fc:60:4b brd ff:ff:ff:ff:ff:ff inet 100.0.0.1/24 brd 100.0.0.255 scope global ens33 valid_lft forever preferred_lft forever inet 100.0.0.254/24 brd 100.0.0.255 scope global secondary ens33 valid_lft forever preferred_lft forever inet6 fe80::5f65:9c3d:d218:7cea/64 scope link valid_lft forever preferred_lft forever2、使用富规则配置端口转发:
[root@localhost /]# firewall-cmd --zone=external --add-rich-rule='rule family=ipv4 destination address=100.0.0.254/24 forward-port port=443 protocol=tcp to-addr=192.168.2.10' success3、验证:
