第二层隧道协议L2TP(Layer 2 Tunneling Protocol)是一种工业标准的Internet隧道协议,它使用UDP的1701端口进行通信。L2TP本身并没有任何加密,但是我们可以使用IPSec对L2TP包进行加密。
l2tp就用xl2tpd,官网:http://www.xelerance.com/services/software/xl2tpd/
IPSec就是openswan,提供IPSec加密,官网是:http://www.openswan.org/code/ ,在centos7 版本后, 提供ipsec 服务包由libreswan替代了openswan。
环境准备
硬件:服务器采用两张网卡,eth0用于连接内网,eth1用于×××网关。
服务器外网地址eth1:10.15.44.132/24
×××:10.0.0.1/16
软件:
openswan:提供IPSec加密
lsof:用于数据访问
ppp:提供用户名、密码 认证
xl2tp:提供L2TP ×××服务
编译环境:
[root@L2TP-××× ~]# yum install -y make gcc gmp-devel xmlto bison flex xmlto libpcap-devel vim-enhanced man一、安装lsof:用于数据访问,没有安装下面配置完openswan验证时可能会报错
[root@L2TP-××× ~]# yum install lsof –y二、安装 配置openswan
1、安装
[root@L2TP-××× ~]# yum -y install openswan2、配置
修改ipsec 主配置文件:
[root@localhost ~]# cp /etc/ipsec.conf{,.20161207bak} [root@localhost ~]# vim /etc/ipsec.conf #注意格式对齐 config setup nat_traversal=yes virtual_private=%v4:10.0.0.0/8,%v4:192.168.0.0/16,%v4:172.16.0.0/12 oe=off protostack=netkey conn %default Forceencaps=yes conn L2TP-PSK-NAT rightsubnet=vhost:%priv also=L2TP-PSK-noNAT conn L2TP-PSK-noNAT #定义一个×××的连接,L2TP-PSK-noNAT是这个连接的名字 authby=secret pfs=no auto=add #ipsec启动后,×××1连接处于等待状态 keyingtries=3 rekey=no ikelifetime=8h keylife=1h type=transport left=10.15.44.132 #vpn服务器外网ip leftprotoport=17/1701 #vpn服务器端口,17指协议号 UDP协议 1701指端口号 right=%any #我们目前这种方式vpn比较简单,所以只配置了一方 rightprotoport=17/%any #enable DPD(Dead Peer Dectection) 死连接检测 dpddelay=40 dpdtimeout=130 dpdaction=clear # leftnexthop=%defaultroute # rightnexthop=%defaultroute [root@localhost ~]# cp /etc/ipsec.secrets{,.20161207bak} [root@localhost ~]# vim /etc/ipsec.secrets #设置IPSec预共享密钥 include /etc/ipsec.d/*.secrets 10.15.44.132 %any: PSK "PASSWORD" #外网IP地址 %any: PSK “预共享密钥” [root@localhost ~]# for each in /proc/sys/net/ipv4/conf/* >do >echo 0 > $each/accept_redirects >echo 0 > $each/send_redirects >done [root@localhost ~]# service ipsec restart #重启IPSec ,此步同ipsec restart,验证 Missing control file /var/run/pluto/pluto.ctl - is pluto running? Starting pluto IKE daemon for IPsec: . [ OK ] [root@localhost ~]# ipsec restart Redirecting to: service ipsec stop Shutting down pluto IKE daemon 002 shutting down Redirecting to: service ipsec start Starting pluto IKE daemon for IPsec: . [ OK ] [root@localhost ~]# ipsec verify #如果正常运行,将会得到类似下面的输出: Verifying installed system and configuration files Version check and ipsec on-path [OK] Libreswan 3.15 (netkey) on 2.6.32-642.el6.x86_64 Checking for IPsec support in kernel [OK] NETKEY: Testing XFRM related proc values ICMP default/send_redirects [OK] ICMP default/accept_redirects [OK] XFRM larval drop [OK] Pluto ipsec.conf syntax [OK] Hardware random device [N/A] Checking rp_filter [ENABLED] /proc/sys/net/ipv4/conf/default/rp_filter [ENABLED] /proc/sys/net/ipv4/conf/lo/rp_filter [ENABLED] /proc/sys/net/ipv4/conf/eth1/rp_filter [ENABLED] rp_filter is not fully aware of IPsec and should be disabled Checking that pluto is running [OK] Pluto listening for IKE on udp 500 [OK] Pluto listening for IKE/NAT-T on udp 4500 [OK] Pluto ipsec.secret syntax [OK] Checking 'ip' command [OK] Checking 'iptables' command [OK] Checking 'prelink' command does not interfere with FIPS [PRESENT] Checking for obsolete ipsec.conf options [OK] Opportunistic Encryption [DISABLED] ipsec verify: encountered 7 errors - see 'man ipsec_verify' for help [root@localhost ~]# chkconfig ipsec on遇到的问题:
1、Two or more interfacesfound, checking IP forwarding [Failed]
[root@localhost ~]# vim /etc/sysctl.conf net.ipv4.ip_forward = 1 [root@localhost ~]# sysctl -p2、Checking that pluto isrunning [Failed]
[root@localhost ~]# cd /var/run/pluto/ [root@localhost pluto]# ipsec pluto [root@localhost pluto]# ls pluto.ctl pluto.pid [root@localhost pluto]# ipsec verify3、ICMP default/send_redirects [NOT DISABLED]
[root@L2TP-××× xl2tpd-1.3.6]# ipsec verify NETKEY: Testing XFRM related proc values ICMP default/send_redirects [NOT DISABLED] Disable /proc/sys/net/ipv4/conf/*/send_redirects or NETKEY will act on or cause sending of bogus ICMP redirects! ICMP default/accept_redirects [NOT DISABLED]根据提示,需要关闭sendredirects和acceptredirects:
[root@L2TP-××× xl2tpd-1.3.6]# sysctl -a |grep -e 'accept_redirects' net.ipv4.conf.all.accept_redirects = 0 net.ipv4.conf.default.accept_redirects = 1 net.ipv4.conf.lo.accept_redirects = 1 net.ipv4.conf.eth0.accept_redirects = 1 net.ipv6.conf.all.accept_redirects = 1 net.ipv6.conf.default.accept_redirects = 1 net.ipv6.conf.lo.accept_redirects = 1 net.ipv6.conf.eth0.accept_redirects = 1 [root@L2TP-××× xl2tpd-1.3.6]#根据网卡数量,选项个数无法确定#,其中也可能会包含IPv6的选项,IPv6的不需要改,可以直接通过下面的脚本把上面显示的所有IPv4的选项全部设置为 0
#!/bin/bash for each in /proc/sys/net/ipv4/conf/* do echo 0 > $each/send_redirects echo 0 > $each/accept_redirects done修改完成后,再进行一次 ipsec 验证即可看到结果
三、安装 配置ppp:提供用户名、密码 认证
[root@localhost ~]# yum -y install ppp [root@localhost ~]# rpm -qa|grep -i ppp rp-pppoe-3.10-16.el6.x86_64 ppp-2.4.5-10.el6.x86_64 [root@localhost ~]# vim /etc/ppp/options.xl2tpd #如果文件不存在直接新建就好了 require-mschap-v2 # 用来支持windows 7,windows8 连接 ms-dns 192.168.100.189 #分配给客户机的DNS地址 ms-dns 202.96.209.133 #ms-wins 192.168.1.2 #ms-wins 192.168.1.4 noccp #asyncmap 0 auth crtscts #lock #hide-password #modem idle 1800 mtu 1410 mru 1410 nodefaultroute debug #name xl2tpd lock proxyarp connect-delay 5000 #lcp-echo-interval 30 #lcp-echo-failure 4 [root@localhost ~]# vim /etc/ppp/chap-secrets #添加用户名/密码(客户端登陆时的用户名密码) # Secrets for authentication using CHAP # client server secret IP addresses # user server password ip justin * 51cto * #justin xl2tpd 51cto * #上面的xl2tpd对应上面etc/ppp/options.xl2tpd文件中的name xl2tpd/etc/ppp/options.xl2tpd 如果文件不存在直接新建或者cp xl2tpd-1.3.6/examples/ppp-options.xl2tpd
四、安装 配置L2TP:提供L2TP ×××服务
1、安装
[root@localhost ~]# yum -y install xl2tpd Loaded plugins: fastestmirror, refresh-packagekit, security Setting up Install Process Loading mirror speeds from cached hostfile * base: mirrors.aliyun.com * extras: mirrors.aliyun.com * updates: mirrors.tuna.tsinghua.edu.cn base | 3.7 kB 00:00 extras | 3.4 kB 00:00 updates | 3.4 kB 00:00 No package xl2tpd available. Error: Nothing to do [root@localhost ~]# wget [root@localhost ~]# yum install -y libpcap-devel^C #xl2tpd的一个依赖,不然编译会报错 [root@localhost ~]# tar zxvf xl2tpd-1.3.6.tar.gz [root@localhost ~]# cd xl2tpd-1.3.6 [root@localhost xl2tpd-1.3.6]# make [root@localhost xl2tpd-1.3.6]# make install [root@localhost xl2tpd-1.3.6]# mkdir /etc/xl2tpd [root@localhost xl2tpd-1.3.6]# cp doc/l2tpd.conf.sample /etc/xl2tpd/xl2tpd.conf [root@localhost xl2tpd-1.3.6]# cp doc/l2tp-secrets.sample /etc/xl2tpd/xl2tp-secrets [root@localhost xl2tpd-1.3.6]# vim /etc/xl2tpd/xl2tpd.conf [global] ;port=1701 #这个在文件是被注释掉的意思,如果要改端口号,改成1723是不行的,l2tp客户端好像不能改端口 [lns default] ip range = 10.0.0.2-10.0.255.254 #vpn连接成功之后,服务器给客户端分配的ip地址,这个不要与局域网ip段重合 local ip = 10.0.0.1 #不是外网地址,也不是内网地址,而是虚拟网关的IP地址,这个没有开启客户端连接时候会提示localhost pppd[3929]: Could not determine local IP address length bit = yes require chap = yes refuse pap = yes refuse authentication = yes ppp debug = yes name = Linux×××server pppoptfile = /etc/ppp/options.xl2tpd [root@localhost xl2tpd-1.3.6]#如果找不到xl2tpd包,需要安装epel源yum install -y epel-release
xl2tpd.conf也可以使用默认示例配置文件examples/xl2tpd.conf,这个文件更加简洁。centos7后的libreswan在global中开启ipsec saref = yes #启用xl2tpd的ipsec支持,listen-addr = 1.2.3.4 #1.2.3.4为对外提供连接的服务器地址
启用包转发
[root@localhost ~]# vim /etc/sysctl.conf net.ipv4.ip_forward = 1 net.ipv4.conf.default.rp_filter = 0 net.ipv4.conf.default.accept_source_route =0 kernel.sysrq = 0 kernel.core_uses_pid = 1 net.ipv4.tcp_syncookies = 1 kernel.msgmnb = 65536 kernel.msgmax = 65536 kernel.shmmax = 68719476736 kernel.shmall = 4294967296 net.core.xfrm_larval_drop = 1 [root@localhost ~]# sysctl -p防火墙配置
[root@localhost ~]# iptables -A INPUT -p udp --destination-port 1701 -j ACCEPT [root@localhost ~]# iptables -t nat -A POSTROUTING -s 10.0.0.0/24 -o eth0 -j MASQUERADE [root@localhost ~]# iptables -A INPUT -j ACCEPT [root@localhost ~]# iptables -A OUTPUT -j ACCEPT [root@localhost ~]# /etc/init.d/iptables save [root@localhost ~]# /etc/init.d/iptables restartiptables -t nat -A POSTROUTING -j MASQUERADE
iptables -t nat -A POSTROUTING -s 10.0.0.0/24 -o eth0 -j MASQUERADE
iptables -A FORWARD -m state --state RELATED,ESTABLISHED -j ACCEPT
iptables -I FORWARD -s 10.0.0.0/24 -j ACCEPT
iptables -I FORWARD -d 10.0.0.0/24 -j ACCEPT
iptables -A FORWARD -j REJECT
iptables -A INPUT -p udp -m state --state NEW -m udp --dport 1701 -j ACCEPT
iptables -A INPUT -p udp -m state --state NEW -m udp --dport 500 -j ACCEPT
iptables -A INPUT -p udp -m state --state NEW -m udp --dport 4500 -j ACCEPT
启动
参数D表示让l2tpd在前台运行,显示整个l2tpd的运行信息,如果不加D,l2tpd在后台运行;其它参数查看目录下的README*/
[root@localhost xl2tpd-1.3.6]# ./xl2tpd -D xl2tpd[2144]: setsockopt recvref[30]: Protocol not available xl2tpd[2144]: L2TP kernel support not detected (try modprobing l2tp_ppp and pppol2tp) xl2tpd[2144]: open_controlfd: Unable to open /var/run/xl2tpd/l2tp-control for reading. [root@localhost xl2tpd-1.3.6]# mkdir /var/run/xl2tpd/ [root@localhost xl2tpd-1.3.6]# touch /var/run/xl2tpd/l2tp-control [root@localhost xl2tpd-1.3.6]# ./xl2tpd -D xl2tpd[2275]: setsockopt recvref[30]: Protocol not available xl2tpd[2275]: L2TP kernel support not detected (try modprobing l2tp_ppp and pppol2tp) xl2tpd[2275]: xl2tpd version xl2tpd-1.3.6 started on localhost.localdomain PID:2275 xl2tpd[2275]: Written by Mark Spencer, Copyright (C) 1998, Adtran, Inc. xl2tpd[2275]: Forked by Scott Balmos and David Stipp, (C) 2001 xl2tpd[2275]: Inherited by Jeff McAdams, (C) 2002 xl2tpd[2275]: Forked again by Xelerance (www.xelerance.com) (C) 2006 xl2tpd[2275]: Listening on IP address 0.0.0.0, port 1701 [root@localhost xl2tpd-1.3.6]# netstat -naptlu | grep xl2tpd udp 0 0 0.0.0.0:1701 0.0.0.0:* 3695/./xl2tpd [root@localhost xl2tpd-1.3.6]# vim /etc/init.d/xl2tpd #!/bin/sh # # xl2tpd This shell script takes care of starting and stopping l2tpd. # # chkconfig: - 80 30 # de script ion: Layer 2 Tunnelling Protocol Daemon (RFC 2661) # # processname: xl2tpd # config: /etc/xl2tpd/xl2tpd.conf # pidfile: /var/run/xl2tpd.pid #Servicename SERVICE=xl2tpd # Source function library. . /etc/rc.d/init.d/functions # Source networking configuration. . /etc/sysconfig/network if [ ${NETWORKING} = "no" ] then exit 0 fi [ -x /usr/local/sbin/$SERVICE ] || exit 0 RETVAL=0 start() { echo -n "Starting $SERVICE: " if [ ! -d /var/run/xl2tpd ] then mkdir /var/run/xl2tpd fi daemon /usr/local/sbin/$SERVICE RETVAL=$? [ $RETVAL -eq 0 ] && touch /var/lock/subsys/$SERVICE echo "" return $RETVAL } stop() { echo -n "Stopping $SERVICE: " killproc $SERVICE RETVAL=$? echo [ $RETVAL -eq 0 ] && rm -f /var/lock/subsys/$SERVICE return $RETVAL } restart() { stop start } # See how we were called. case "$1" in start) start ;; stop) stop ;; status) status $SERVICE RETVAL=$? ;; restart|reload) restart ;; condrestart) [ -f /var/lock/subsys/$SERVICE ] && restart || : ;; *) echo "Usage: $SERVICE {start|stop|status|restart|reload|condrestart}" exit 1 esac [root@localhost xl2tpd-1.3.6]# chmod +x /etc/init.d/xl2tpd [root@localhost xl2tpd-1.3.6]# chkconfig --add xl2tpd [root@localhost xl2tpd-1.3.6]# chkconfig --add pppoe-server [root@localhost xl2tpd-1.3.6]# chkconfig --add ipsec [root@localhost xl2tpd-1.3.6]# chkconfig xl2tpd on [root@localhost xl2tpd-1.3.6]# chkconfig pppoe-server on [root@localhost xl2tpd-1.3.6]# chkconfig ipsec on [root@localhost xl2tpd-1.3.6]# /etc/init.d/pppoe-server restart [root@localhost xl2tpd-1.3.6]# /etc/init.d/ipsec restart [root@localhost xl2tpd-1.3.6]# /etc/init.d/xl2tpd restart [root@localhost xl2tpd-1.3.6]# /etc/rc.d/rc.local /etc/init.d/xl2tpd start [root@localhost xl2tpd-1.3.6]#日志信息:
[root@localhost xl2tpd]# tail -f /var/log/messages Dec 9 12:13:02 localhost xl2tpd[2457]: Written by Mark Spencer, Copyright (C) 1998, Adtran, Inc. Dec 9 12:13:02 localhost xl2tpd[2457]: Forked by Scott Balmos and David Stipp, (C) 2001 Dec 9 12:13:02 localhost xl2tpd[2457]: Inherited by Jeff McAdams, (C) 2002 Dec 9 12:13:02 localhost xl2tpd[2457]: Forked again by Xelerance (www.xelerance.com) (C) 2006 Dec 9 12:13:02 localhost xl2tpd[2457]: Listening on IP address 0.0.0.0, port 1701五、测试拨号是否成功
端口测试:
一般我们用telnet测试端口连通性,但是telnet使用的是tcp协议,也就是说telnet只能检测tcp的这个端口打开了没。除了telnet以外,还有一个命令nc也可查看端口是否打开,它可以检测tcp和udp端口连通性。
[root@localhost ppp]# nc -vuz 192.168.100.243 1707 Connection to 192.168.100.243 1707 port [udp/vdmplay] succeeded! [root@localhost ppp]# nc -vuz 10.10.2.80 80 Connection to 10.10.2.80 80 port [udp/http] succeeded! [root@localhost ppp]#-i<延迟秒数> 设置时间间隔,以便传送信息及扫描通信端口。
-l 使用监听模式,管控传入的资料。
-n 直接使用IP地址,而不通过域名服务器。
-o<输出文件> 指定文件名称,把往来传输的数据以16进制字码倾倒成该文件保存。
-p<通信端口> 设置本地主机使用的通信端口。
-r 乱数指定本地与远端主机的通信端口。
-s<来源地址> 设置本地主机送出数据包的IP地址。
-u 使用UDP传输协议。
-v 显示指令执行过程。
-w<超时秒数> 设置等待连线的时间。
-z 使用0输入/输出模式,只在扫描通信端口时使用。
客户端连接测试:
windows server 2008下:L2TP客户端设置
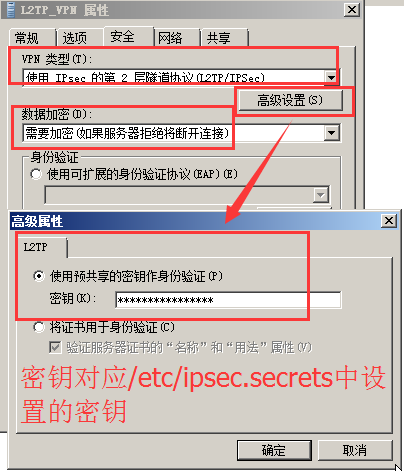
1、右键选择创建好的×××连接属性,点击“安全”
×××类型:使用IPsec 的第2层隧道协议(L2TP/IPsec)
数据加密:需要加密(如果服务器拒绝将断开连接)
高级设置:使用预共享密钥作为身份验证,密钥对应/etc/ipsec.secrets中设置的密钥
2、修改注册表:运行:regedit.exe
开始>>运行>>regedit.exe找到下面这个路径:
HEKY_LOCAL_MACHINE/SYTEM/CUrrentCOntrolSet/Services/RasMan/Parameters,新增或修改ProhibitIpSec的值(类型DWORD)为1
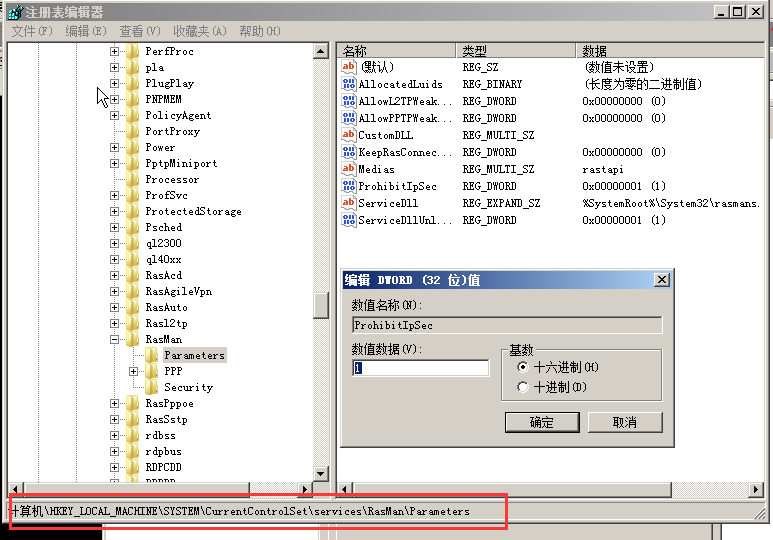
完成后测试连接是否正常,若仍提示连接不上,重启电脑再次尝试。
如果还是无法连接查看服务端日志/var/log/messages
