Host-A IP:192.168.56.129OS:RHEL5.932bitService: telnet-server Host-B IP:192.168.56.128OS:RHEL5.932bitService: telnet-client 在HostA上查看网卡信息 # ifconfig eht0eth0 Link encap:Ethernet HWaddr 00:0C:29:CC:30:9Ainet addr:
Host-A
IP:192.168.56.129 OS:RHEL5.9 32bit Service:telnet-server
Host-B
IP:192.168.56.128 OS:RHEL5.9 32bit Service:telnet-client
在HostA上查看网卡信息
# ifconfig eht0 eth0 Link encap:Ethernet HWaddr 00:0C:29:CC:30:9A inet addr:192.168.56.129 Bcast:192.168.56.255 Mask:255.255.255.0 inet6 addr: fe80::20c:29ff:fecc:309a/64 Scope:Link UP BROADCAST RUNNING MULTICAST MTU:1500 Metric:1 RX packets:4914 errors:0 dropped:0 overruns:0 frame:0 TX packets:3705 errors:0 dropped:0 overruns:0 carrier:0 collisions:0 txqueuelen:1000 RX bytes:2419811 (2.3 MiB) TX bytes:276508 (270.0 KiB) Interrupt:67 Base address:0x2024
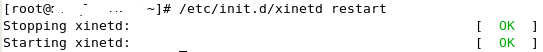
启动telnet服务

安装wireshark抓包工具
#yum install -y wireshark #yum install -y wireshark-gnome //把命令行工具和gnome图形工具的包一起安装上
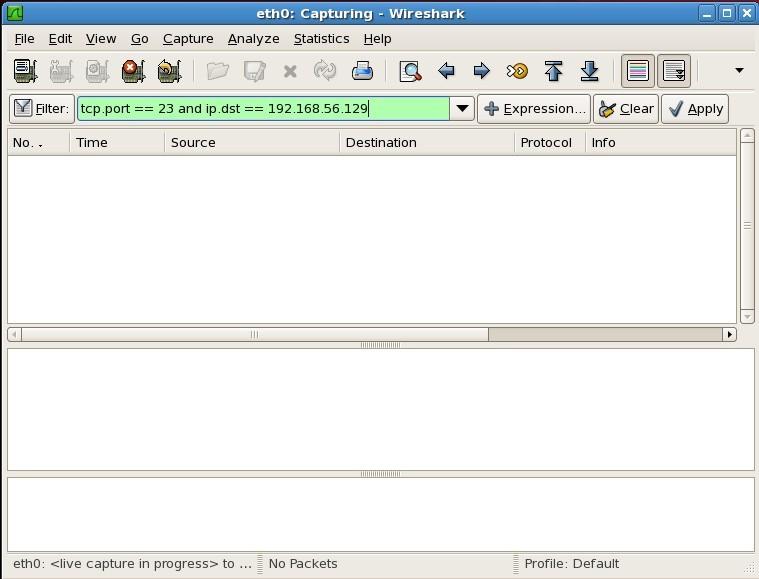
开启wireshark抓包,为了方便分析包信息,写了过滤规则tcp.port == 23 and ip.dst == 192.168.56.129
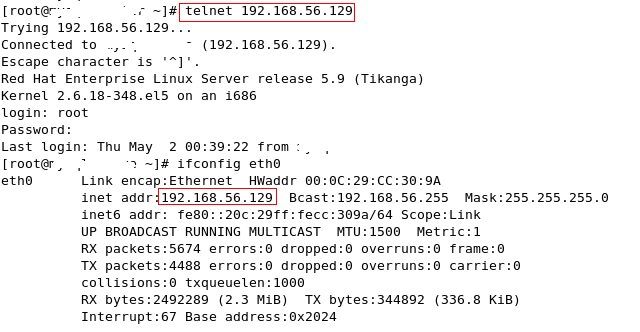
在192.168.56.128机器上以root用户telnet登录192.168.56.129,首先查看网卡信息
#ifconfig eth0 eth0 Link encap:Ethernet HWaddr 00:0C:29:E8:F9:FE inet addr:192.168.56.128 Bcast:192.168.56.255 Mask:255.255.255.0 inet6 addr: fe80::20c:29ff:fee8:f9fe/64 Scope:Link UP BROADCAST RUNNING MULTICAST MTU:1500 Metric:1 RX packets:3518 errors:0 dropped:0 overruns:0 frame:0 TX packets:4232 errors:0 dropped:0 overruns:0 carrier:0 collisions:0 txqueuelen:1000 RX bytes:276736 (270.2 KiB) TX bytes:2356751 (2.2 MiB) Interrupt:67 Base address:0x2024以root用户登录密码为redhat,成功登录!
在192.168.56.129用wireshark抓包
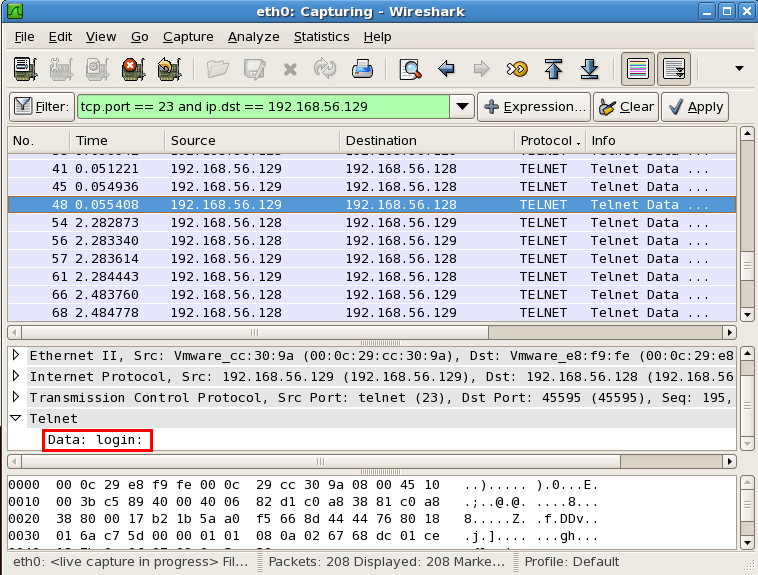
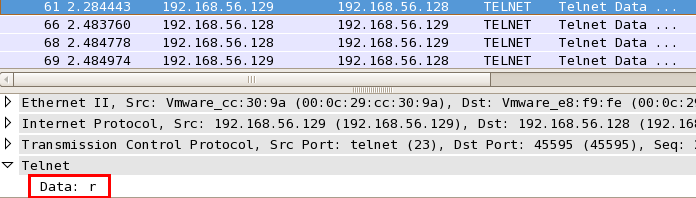
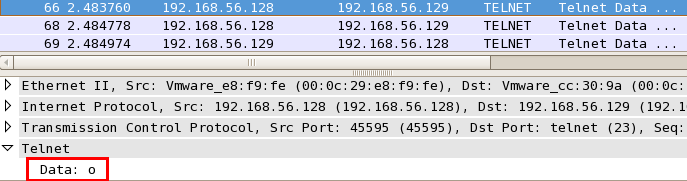
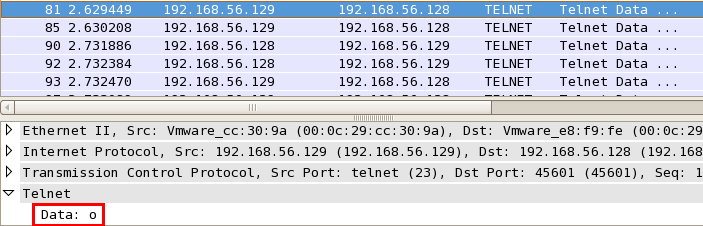
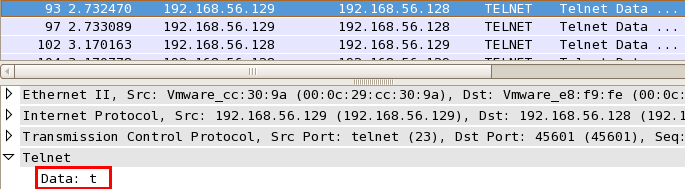
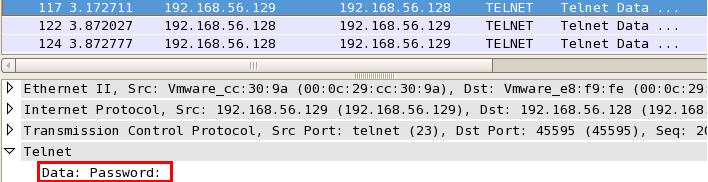
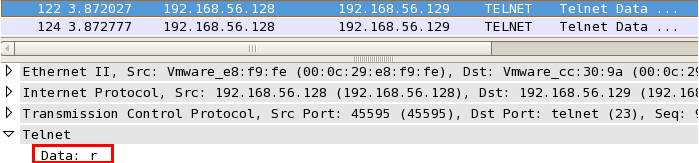
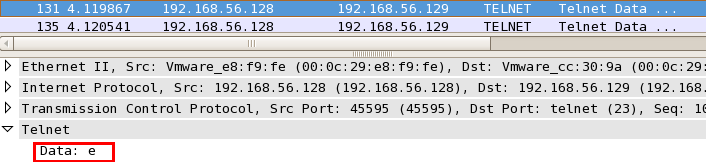
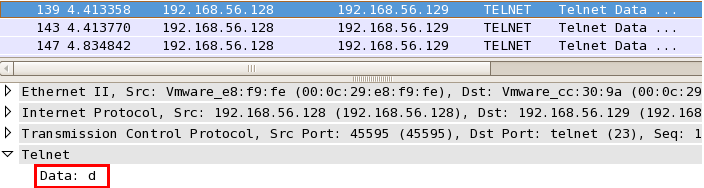
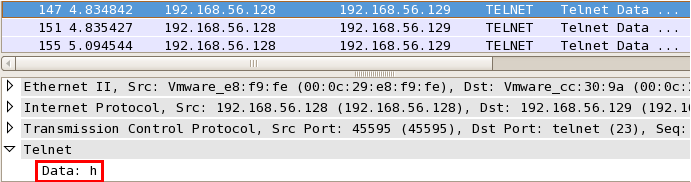
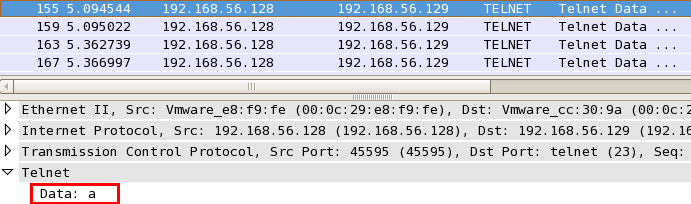
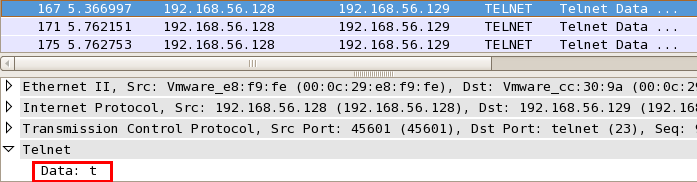
可以清楚的看到用户名为root密码为redhat,所以说telnet是一个明文传输的协议极其不安全,建议使用ssh v2版本。
以上操作证明了telnet的明文传输密码,协议不经过任何加密措施,希望让大家有深刻的认识。除此还有ftp、rlogin、smtp、pop3同样的明文传输密码,但最危险的还是telnet因为一旦劫获的就直接是操作系统的用户名和密码。
【转自:美国高防站群服务器 http://www.558idc.com/mggfzq.html 复制请保留原URL】